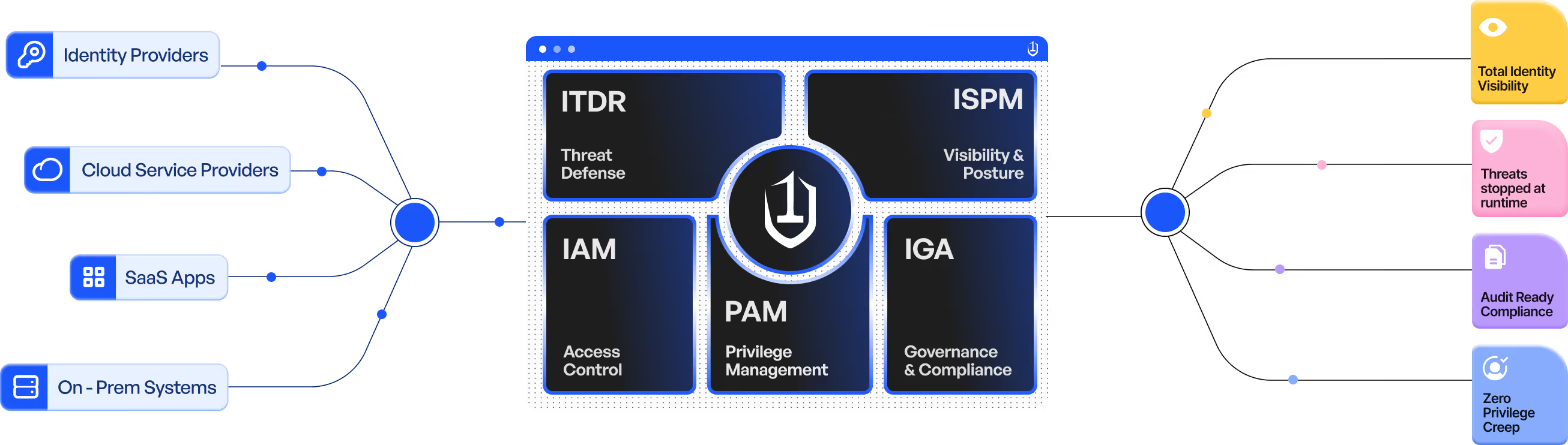
The Unified Identity Fabric by Unosecur
Unosecur stitches together your current tools, workflows, and teams into a cohesive whole. Rather than replacing existing systems, it connects them, adds a layer of insight, protection, and control across your identity ecosystem.
Why identity gaps keep growing
.avif)
Invisible Access Sprawl
Dormant accounts and overlooked permissions silently widen your attack surface, giving attackers room to move before anyone notices.
.avif)
Toxic Combinations
Low-risk permissions silently combine across systems into breach-ready access paths that no single tool can detect.
.avif)
Fragmented Identity Signals
Your identity data lives across dozens of tools and consoles, so no team can correlate who is doing what, where, or when.
Legacy tools handle fragments. We secure the full lifecycle
Attackers move fast. You need to be faster.
Unosecur’s unified identity fabric stops identity threats at runtime, closing gaps, fixing risky permissions, and securing every environment without slowing your team down.
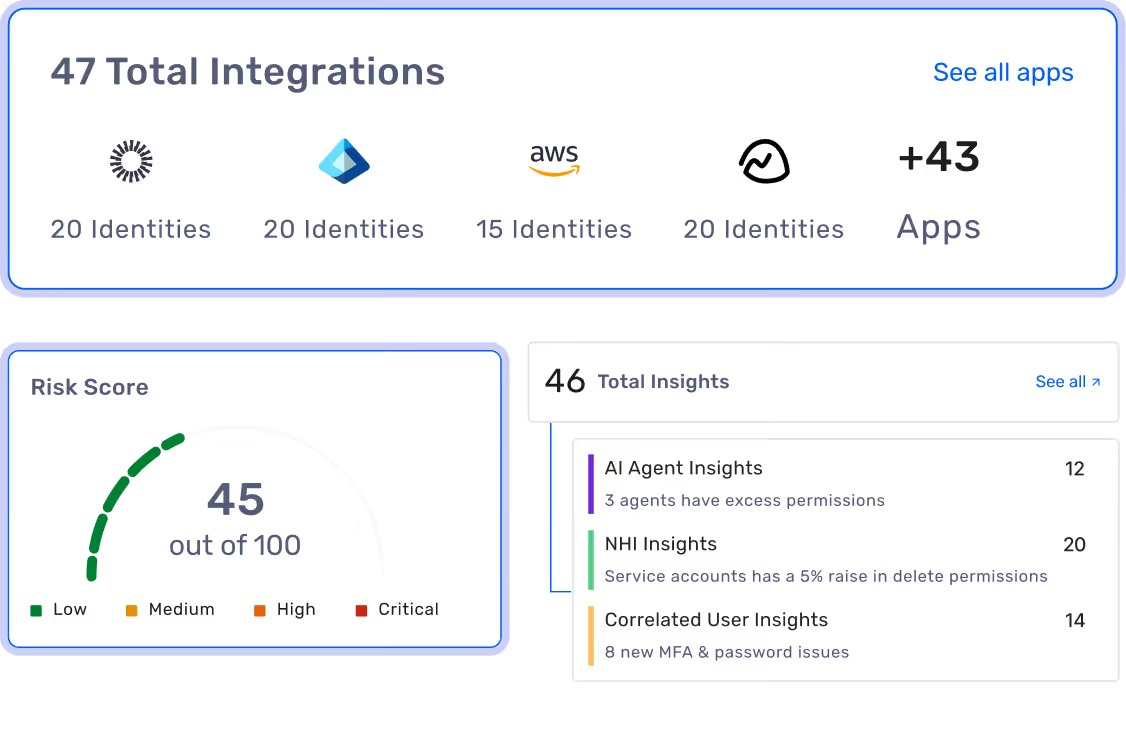
See every identity. Even the ones you've forgotten about.
- Automated discovery across 100+ integrations
- Full visibility into service accounts, shared credentials, and NHIs
- Continuous behavioural pattern tracking for anomalies
- Risk-scored on discovery, so you know what to tackle first
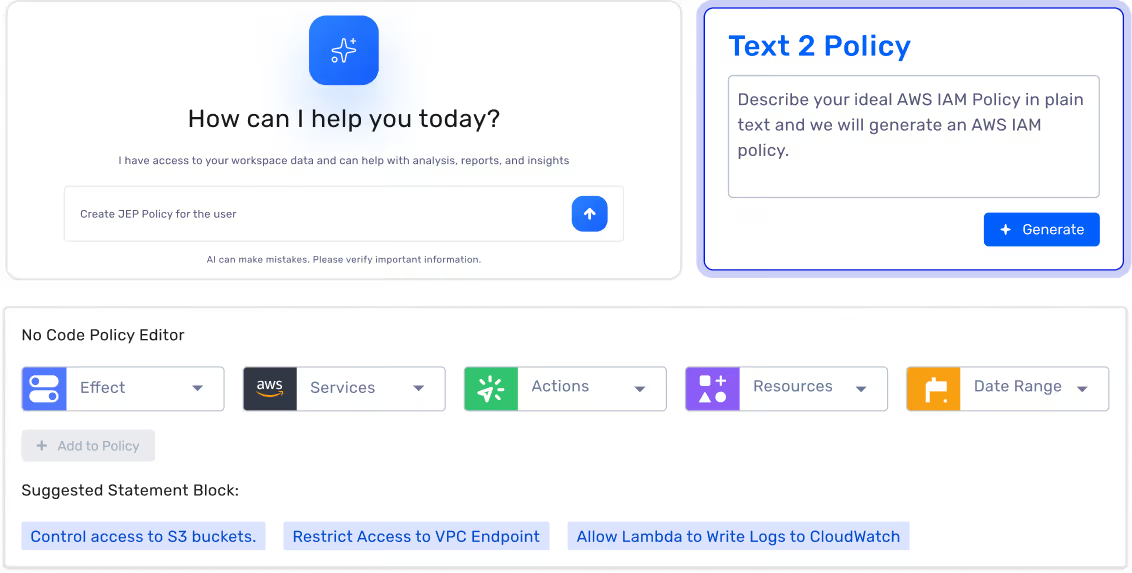
Policy enforcement without the engineering overhead.
- Automated access provisioning and revocation based on policies
- Granular, role specific security policies
- Workflow builder with no code dependencies
- Least privilege enforced consistently across every environment
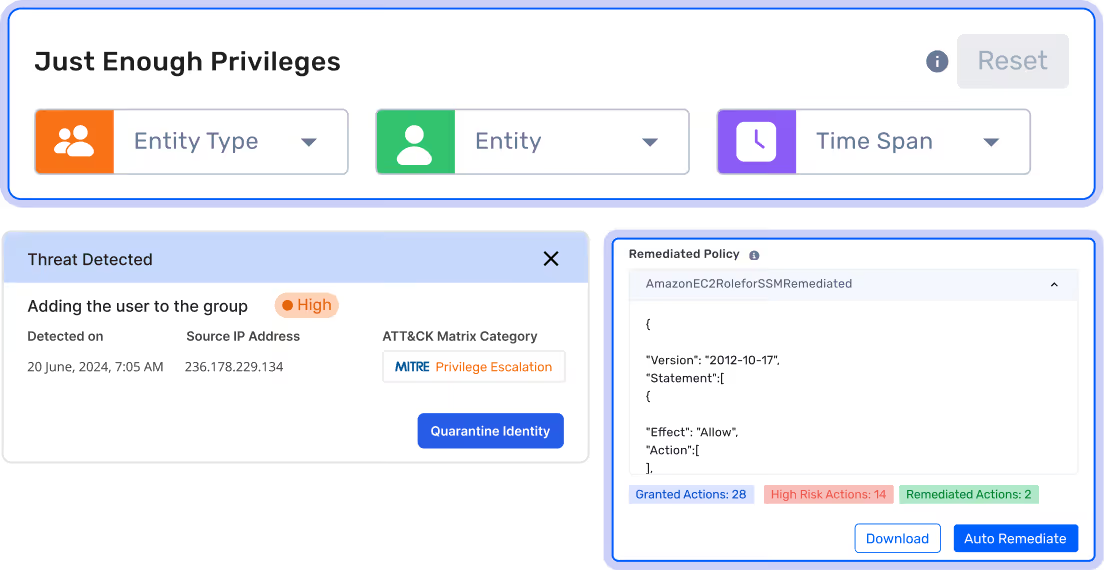
Risk closed before it becomes a breach.
- Instant automated threat response across your stack
- Activity based access control that adapts to real usage
- Scales to match organization growth
- Consistent policy enforcement across all connected environments.
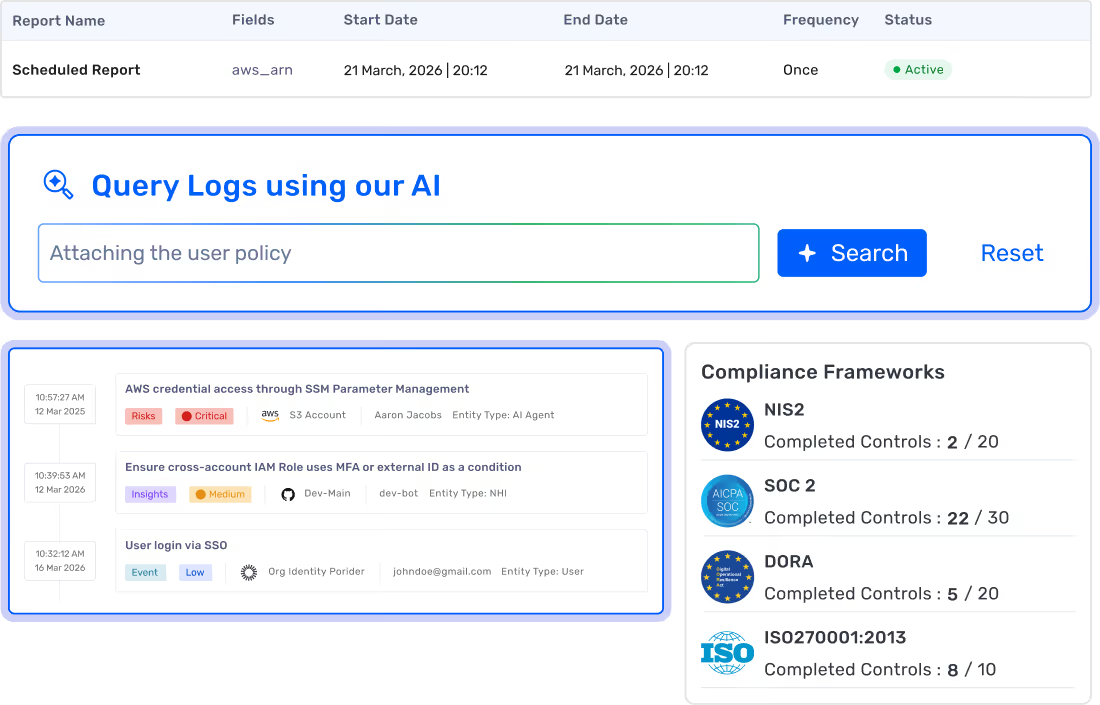
Every action logged, every audit answered before it begins.
- Complete access permission and activity analysis across all identity types permissions and activities
- Customisable, scheduled report generation for any compliance framework
- Tamper-evident trails built for SOC2, HIPAA, ISO, GDPR, NIS2 and DORA
- Powerful natural language querying (NLQ) for complex audit logs
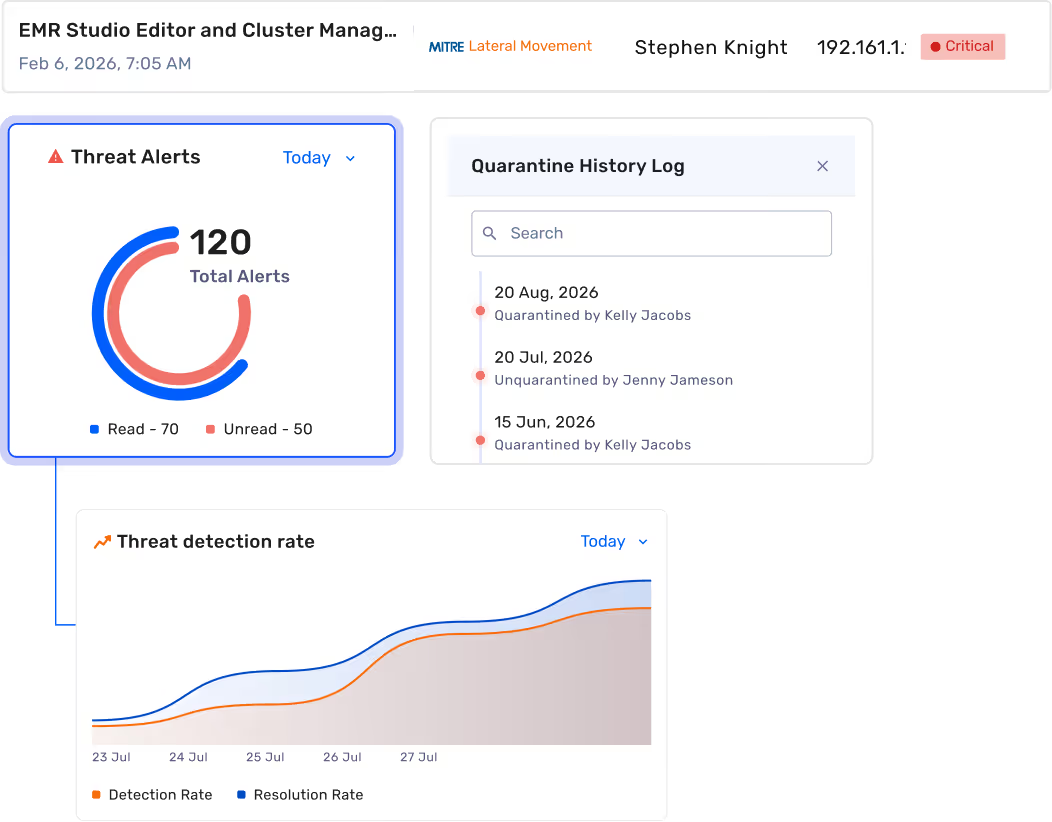
Full-context threat detection across every environment.
- MITRE ATT&CK and machine learning driven threat detection
- In-depth forensic analysis tools for investigation
- Run-time alerts and notifications for suspicious activities
- Risk-based prioritization to surface high-risk actions first
What unified context looks like in practice
When every identity signal flows through one system, insights emerge that no single tool can generate.
See the blast radius before it happens
Unosecur maps access paths and the blast radius of every identity, so you understand the real-world impact of a compromise before an attacker does.
Patterns spanning your environment
Unosecur correlates activity across every connected tool, surfacing anomalies, trends, and risks that stay invisible when each tool only sees its own slice.
Know exactly what to do next
Unosecur doesn't just surface findings; it prioritises them by real-world impact and tells you precisely which action will reduce the most risk, right now.
Unosecur Integrates across your Tech Stack
From cloud providers to collaboration tools, Unosecur plugs into the apps your enterprise runs on. Seamless integrations mean faster visibility, stronger controls, and fewer blind spots.





















































Get a personalized demo
Ready to see Unosecur in action?




