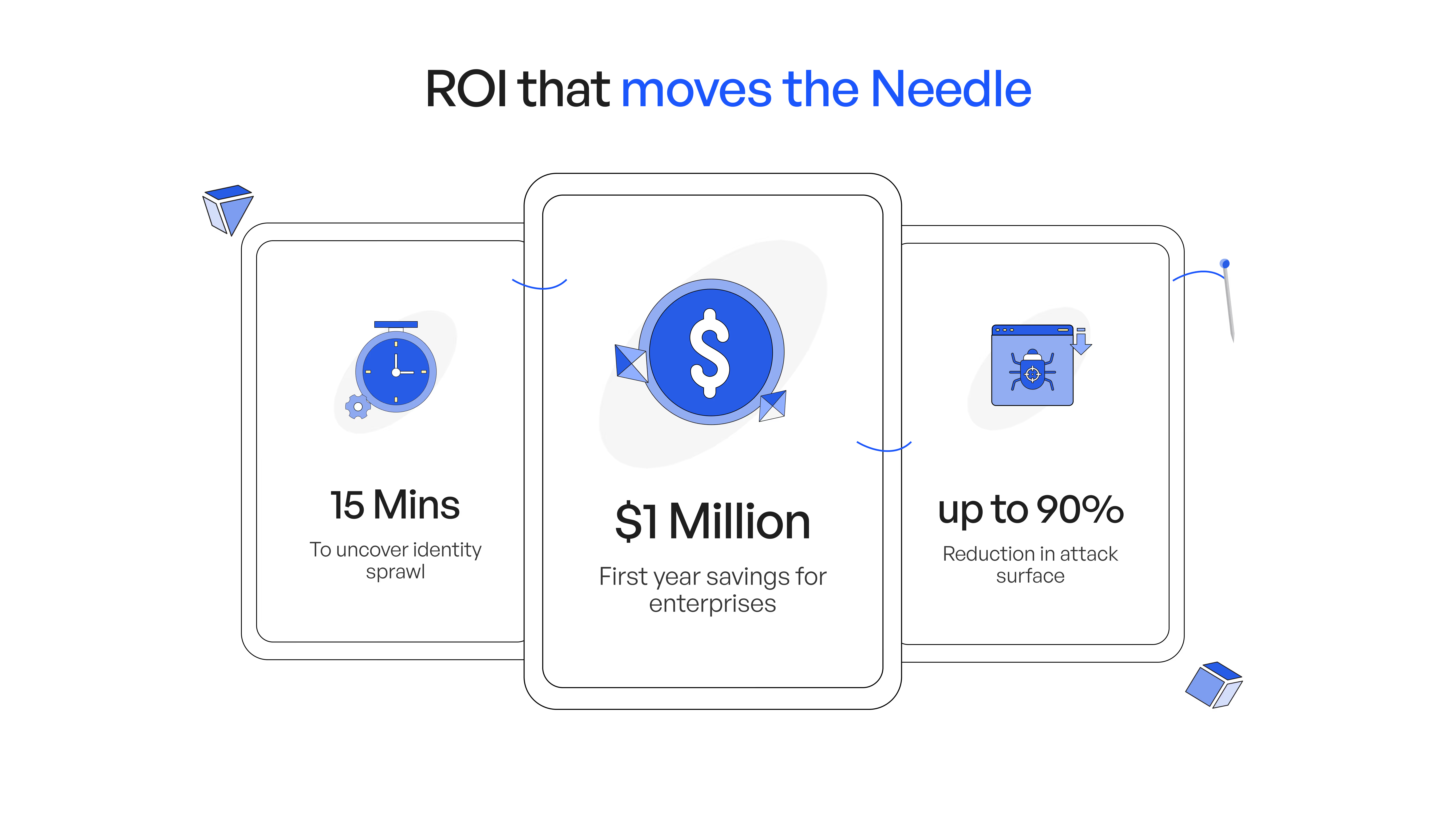
Unified Identity Security for the Agentic Enterprise
Discover, govern, and enforce least privilege for every AI agent, NHI and human identity across multi-cloud, SaaS, IdPs, and on-prem in run-time.










%20(1).avif)





80% of Security Incidents are based on stolen credentials
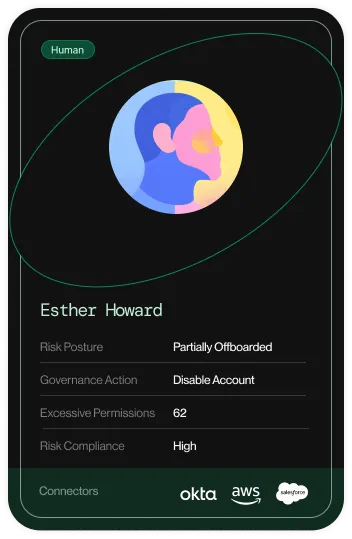
Attackers exploit compromised access across employees, service accounts, API tokens, and AI agents alike. As NHIs multiply and AI agents gain access to critical systems, identity security has become the highest-stakes challenge in modern enterprises.
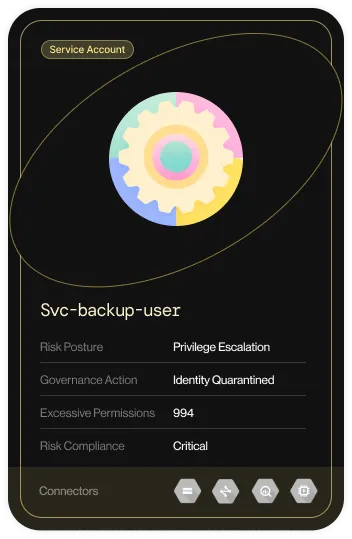
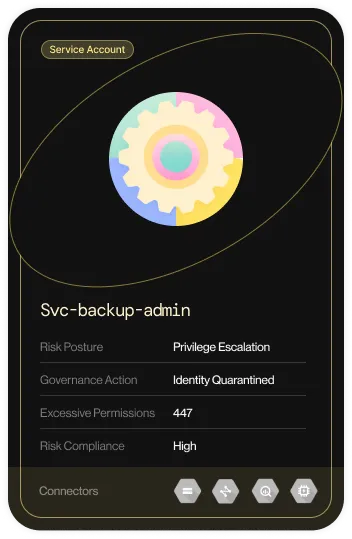
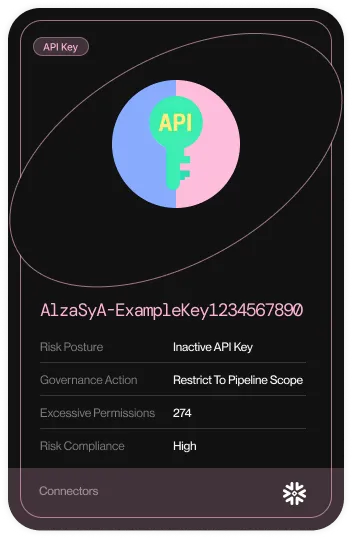
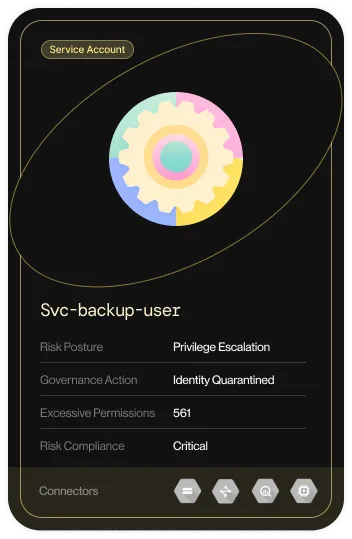
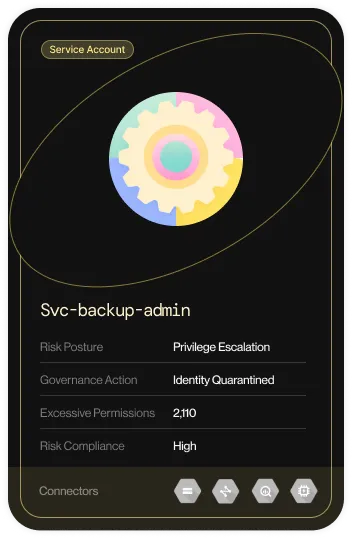
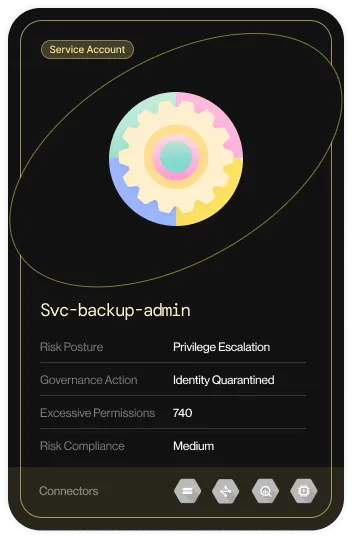
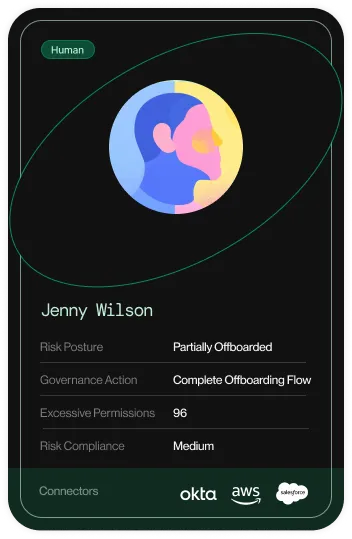
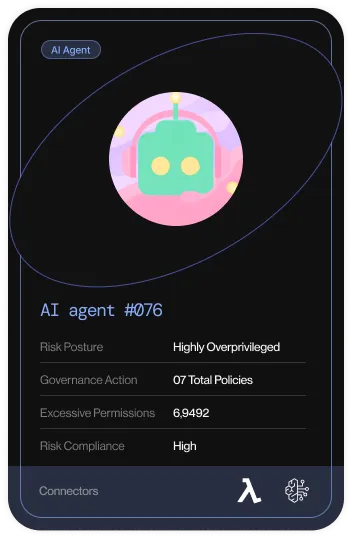
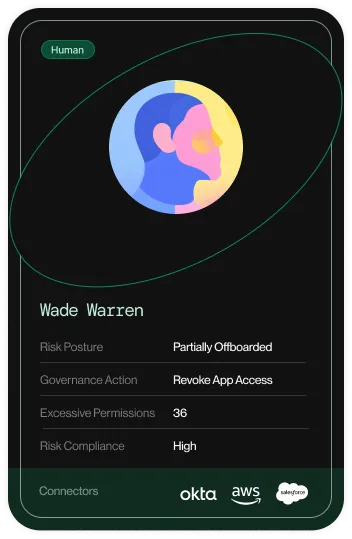
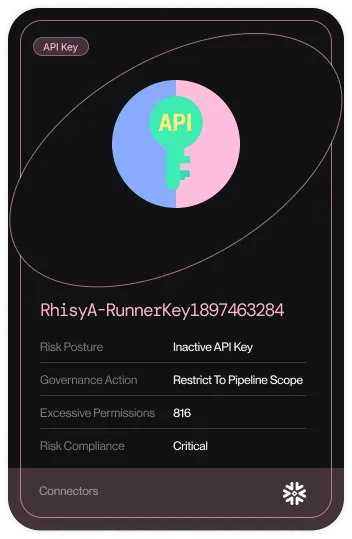
Excessive Permissions are Everywhere
Access sprawl from old roles and dormant privileges leave accounts dangerously overprivileged.
Who has access to What and Why?
Limited visibility and siloed systems create blind spots that attackers easily exploit.
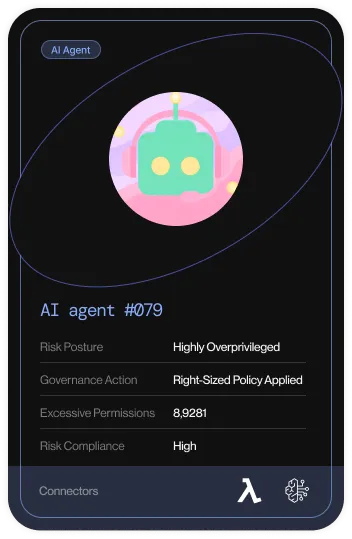
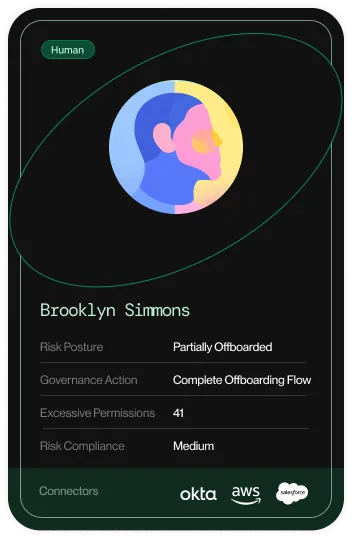
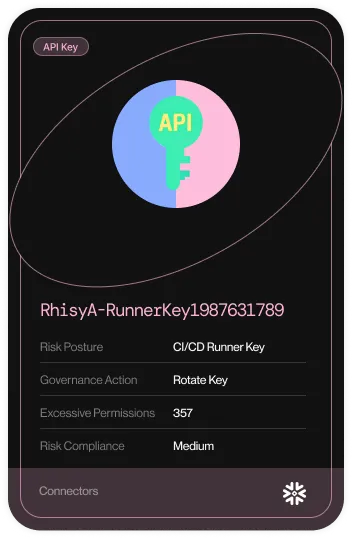
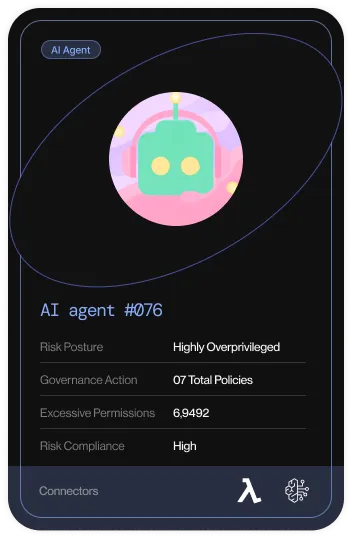
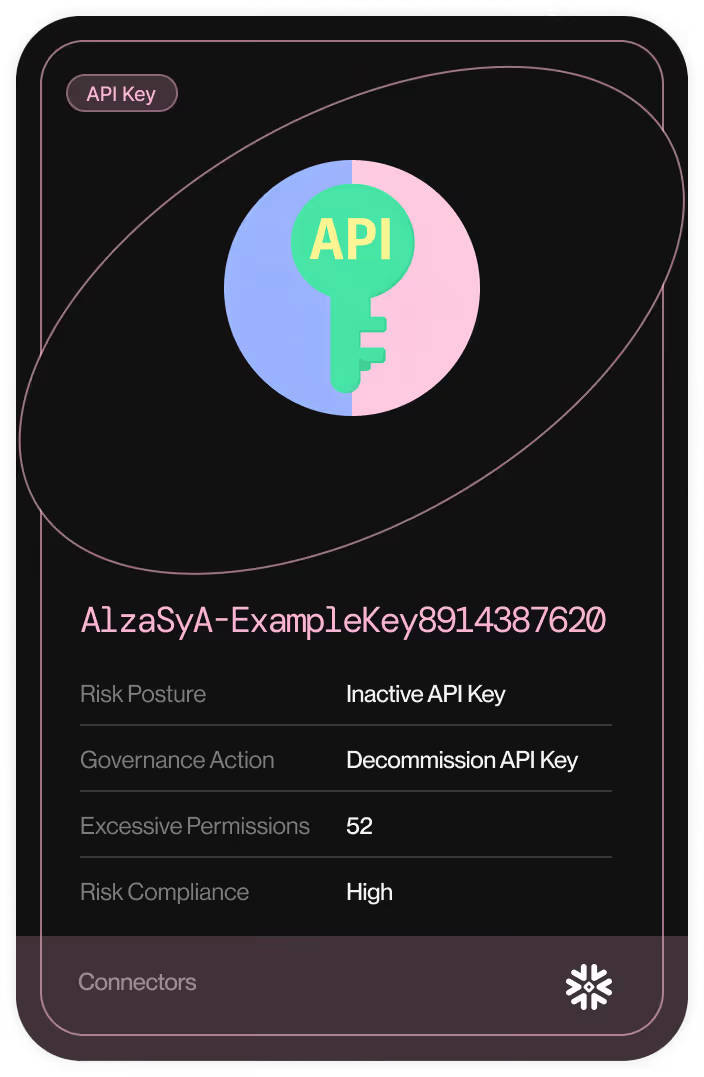
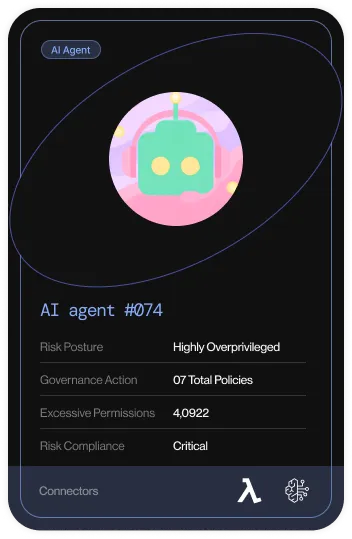
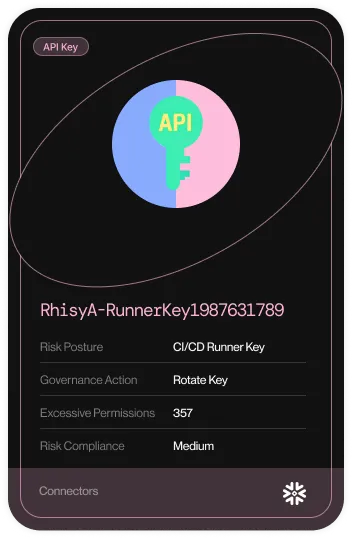
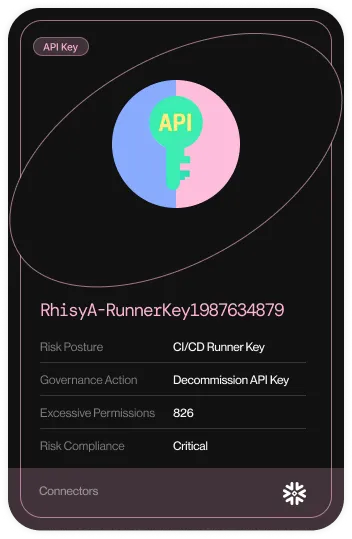
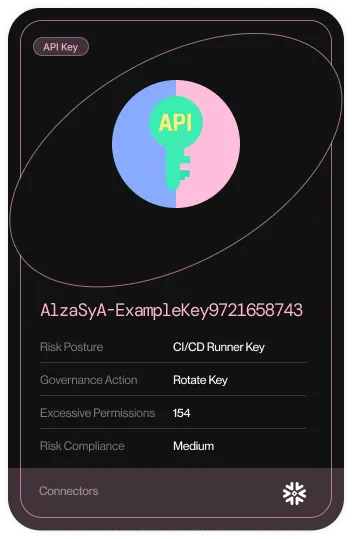
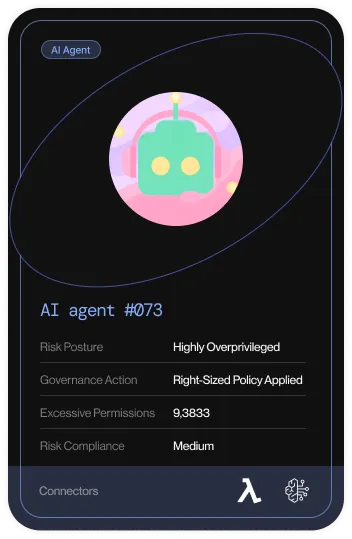
NHIs and AI Agents Are Exploding in Number
Service accounts, API keys, OAuth tokens, and AI agents outnumber humans yet remain unprotected.
Unosecur’s Unified Identity Fabric
A single, adaptable framework that gives your security team run-time insights into every human's, NHI's, and AI agent's lifecycle, no matter where they live or what they access.
See every identity
Activity-based, identity-centric visibility across your tech stack with no blind spots.
Shrink the blast radius
Reduce risk by detecting anomalies early, containing breaches at runtime.
Execute effortlessly
Enforce least privilege with a human-in-the-loop or automated remediation workflows.
The Unosecur Approach to Identity Security
From discovery to remediation, Unosecur continuously analyzes identity activity. Security teams receive prioritized, context-rich insights aligned to MITRE ATT&CK so they can detect, investigate, and stop identity threats quickly.
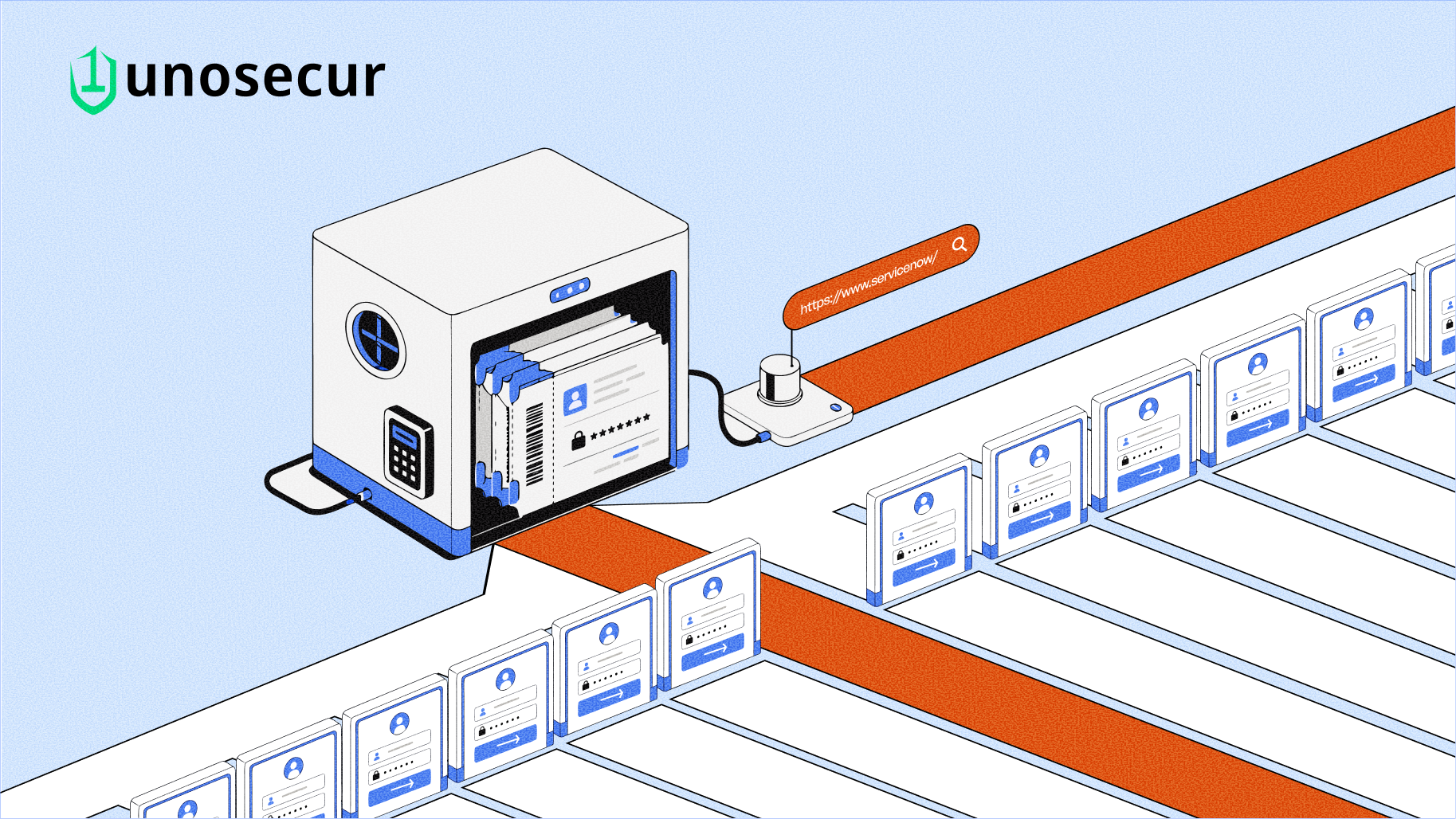
Discover and Analyze
Create a complete inventory of humans, non-humans, and AI agents that traditional IAM tools often miss. Map every access path through graph-powered visualizations to understand how identities interact across your environment.
.avif)
Monitor and Control
Continuously monitor activity across humans and NHIs, including service accounts and AI agents. Track access behavior and maintain clear visibility into how identities interact with systems and resources.
.avif)
Audit and Govern
Enforce least privilege with AI-driven policies, automated access reviews, CIS benchmarks and identity compliance across SOC2, ISO, PCI-DSS, NIS2 and DORA.
.avif)
Respond and Remediate
Block account takeovers, NHI credential abuse, and rogue AI agent activity in real time. Unosecur quarantines suspicious identities instantly within your runtime environment.
.avif)
Unosecur Integrates across your Tech Stack
Unosecur connects to every layer of your stack, including cloud providers, SaaS apps, Identity providers, CI/CD pipelines, and AI platforms. With native support for MCP-connected AI agents via the Unosecur MCP Gateway, your AI agent security is covered from day one.





















































Trusted By Security-First Teams Worldwide
Everything you Need to Know

Yes. Unosecur is available as both a public SaaS offering and a self-hosted version that can be deployed within your own environment or in an air-gapped setup.
We run it in isolated environments bound by data sovereignty and data residency laws
Yes. While IGA and IAM provide a baseline, they leave blind spots such as locally managed users, shadow admins, AI agents, and non-human identities (NHIs) that aren't protected by MFA. Unosecur leverages native APIs rather than traditional integration protocols. Furthermore, Unosecur doesn't just take a "snapshot in time"; it analyzes activity and behavior to uncover and prioritize advanced identity risks and maintain identity hygiene.
Unosecur hardens Azure, Entra ID, and other Microsoft solutions through deep connectors. Key use cases and outcomes from past Proof of Values (PoVs) include identifying partially offboarded Entra ID admins, detecting unused Service Principals, and revealing that 80% to 90% of granted permissions remain unused. While Microsoft provides various native security services, Unosecur leverages advanced techniques and an intelligence layer to reduce risk by uncovering hidden blind spots before they can be exploited.
Yes. Unosecur uses a lightweight agent to integrate with on-premises systems, ensuring you do not need to open up your firewall.
Yes. Unosecur can be deployed directly within your AWS environment and features native connector for many AWS services.
Unosecur is hosted in various regions worldwide to ensure data remains within specific jurisdictions for residency and compliance reasons. Public SaaS is currently available in Germany, India, and several other regions.
Actionable intelligence for you
Your source for the latest insights and updates on advanced security solutions.
Ready To Secure Your Identities?






.avif)

.avif)

.avif)



.avif)

.avif)

.avif)