When your security stack was built, an identity meant a person. Maybe a service account or two. The detection logic, the behavioral baselines, and the alert thresholds were all calibrated for that world. That world is gone. Today, your environment contains human users, tokens, shared accounts, OAuth applications, third-party integrations, and a growing fleet of AI agents, all operating simultaneously across the cloud, SaaS, and on-prem environments. Each one carries access. Each one carries risk. And most of them were never accounted for when your detection coverage was designed. The result is not a gap. It is a blind spot at scale. And blind spots are exactly where attackers live.
According to the CrowdStrike 2025 Global Threat Report, identity-based intrusions are now the dominant attack pattern across cloud environments. Stolen credentials, session token abuse, and privilege escalation through non-human identities are driving the majority of breaches, not because defenses do not exist, but because they are not looking in the right places. Today, Unosecur closes that. Introducing SaaS Findings: detection rules running across 50+ integrations, covering every identity type in your environment, turning over 25,000 unique detection scenarios into security coverage that leaves no stone unturned.
Why existing detection falls short
Identity security has always evolved in response to the last attack. Perimeter first. Then endpoints followed by cloud IAM. SaaS platforms and AI agents were added to enterprise environments faster than detection logic could keep up and were treated as extensions of existing infrastructure rather than as entirely new identity surfaces with their own risk profiles. The consequence is a generation of tools that are precise within a narrow scope and blind everywhere else. They detect what they were built to detect. They miss what they were never designed to see.
Over 25,000 detection scenarios. Every identity. Every surface.
Over 25,000 unique scenarios are now covered across your environment. These are not generic alerts or threshold-based noise. These are specific, context-aware detection logic mapped to real attack patterns and identity behaviors across 50+ integrations.
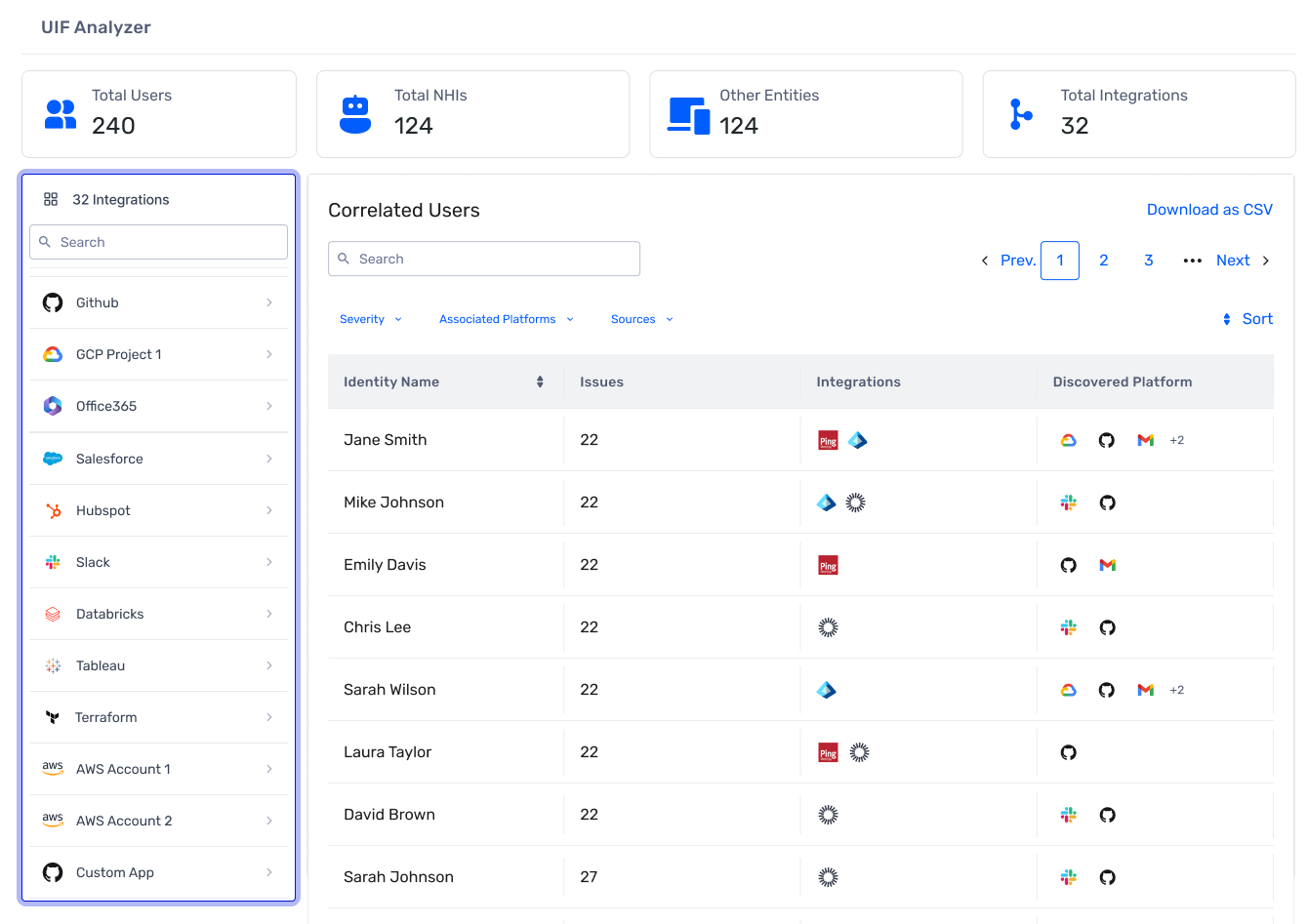
Unosecur SaaS Findings covers:
- Authentication and session threats, including MFA fatigue attacks, token usage without prior login, legacy authentication abuse, and concurrent logins from distant locations across Okta, Microsoft Entra ID, Salesforce, AWS, GCP, and more.
- Behavioral anomalies, including user behavior baseline deviations, abnormal activity volumes, unusual API usage patterns, rapid context switching, and human accounts behaving like service accounts, are all measured against individual baselines rather than static thresholds.
- Privilege escalation detection covering 64 named AWS IAM escalation paths, both single-step and multi-step, GCP service account abuse chains including service account impersonation techniques and token forgery, self-approval attempts, permission boundary removal, and chained escalation sequences across cloud and SaaS.
- Lateral movement and reconnaissance, including sensitive data first access, identity infrastructure access, cross-region jumping, backup and backup system access, and the enumeration behavior that precedes most large-scale exfiltration events.
- SaaS-specific threats covering GitHub repository exposure, OAuth scope abuse, Okta admin action anomalies, Atlassian suspicious activity, programmatic access anomalies, and app installation anomalies across the platforms your teams use every day.
- AI agent security with 60+ categories of purpose-built detection rules covering the OWASP Top 10 for LLM applications mapped to identity behavior, because AI agents are identities, and they need to be treated like one.
AI agents are identities. We treat them that way.
Unosecur is built on a simple principle: every identity in your environment deserves the same depth of detection coverage, whether it is a human user, a non-human identity, or an AI agent. Today, AI agents hold credentials, call APIs, access sensitive data, and operate autonomously at machine speed. When their behavior is manipulated, they continue to function apparently normally while the damage accumulates beneath the surface. The attack vectors are active and being exploited today.
- Prompt injection redirects an agent's actions by inserting malicious instructions into its context.
- Memory poisoning gradually normalizes a backdoor behavior until it registers as baseline.
- Compromise propagation uses a single compromised agent as a launchpad into the broader multi-agent pipeline.
Unosecur detects all of these. Our 60+ categories of agent detection rules include AGENT_PROMPT_INJECTION_DETECTED, AGENT_MEMORY_POISONING, AGENT_HITL_OVERWHELMING, and AGENT_COMPROMISE_PROPAGATION, covering the full range of privilege, credential, and behavioral threats specific to AI agents. If you are running AI agents in production, you have identities operating inside your environment that most security platforms have only recently begun to account for. That changes today. The question security teams should be asking is not whether these threats are real. They are. The question is whether your platform will catch them before the damage is done. The answer depends entirely on whether your detection was built for the identity surface you have today, not the one you had a year ago.
What this means for enterprises
For enterprises running workloads across cloud and SaaS, the exposure is broad. A misconfigured service account in AWS, an OAuth application with excessive scope in Google Workspace, a developer's GitHub token behaving anomalously at 2 am, an AI agent whose actions have been quietly redirected by an injected instruction. Each of these is a detection moment. Each of them is invisible to a platform that was not built to see it.
The recent Vercel breach made this concrete. No zero-day was used. No malware touched an endpoint. An attacker compromised a Context.ai employee via an infostealer, used that foothold to access a Google Workspace account through an existing OAuth grant, pivoted into Vercel's internal environments, and enumerated environment variables holding production secrets. Four identity hops. Every action is authenticated. Nothing that traditional perimeter or endpoint tooling could see.
Here is where Unosecur would have fired at each hop:
- When the OAuth grant to Context.ai was established with broad Workspace scopes, SESSION_OAUTH_CONSENT_UNUSUAL and ATTACK_OAUTH_SCOPE_ABUSE would have flagged the unusual consent pattern for review.
- When the attacker pivoted from Workspace into Vercel's environments through that grant, LATERAL_IDENTITY_INFRA_ACCESS would have detected access to identity infrastructure outside the identity's normal scope.
- When environment variable enumeration began, LATERAL_RECONNAISSANCE_ACTIVITY would have caught the pattern, and LATERAL_SENSITIVE_DATA_FIRST_ACCESS would have fired the moment a credential-holding variable was touched for the first time.
Multiple detection moments across four identity hops, each surfacing a high-context alert for your security team to act on. The chain was not unstoppable. It was just unseen. That is what over 25,000 detection scenarios look like in practice. Not coverage for coverage's sake. Accuracy at every stage, across every identity, with no blind spots left unturned.
One platform. Every identity. No blind spots.
Unosecur's unified identity fabric now detects threats across human users, service accounts, tokens, shared accounts, OAuth applications, third-party integrations, and AI agents, spanning 50+ integrations including AWS, Azure, GCP, Okta, GitHub, Bitbucket, Atlassian, and more. For the first time, every identity in your environment: human, non-human, and AI agent, is under the same detection coverage, on the same platform, with no surfaces left unmonitored.
See what your current stack is missing
If your environment includes AI agents, and at this point most do, there is a high probability that you have identities operating with elevated access and zero dedicated detection coverage elsewhere. We would like to show you what is currently invisible to your security stack. Book a 30-minute demo with the Unosecur team.








.avif)




