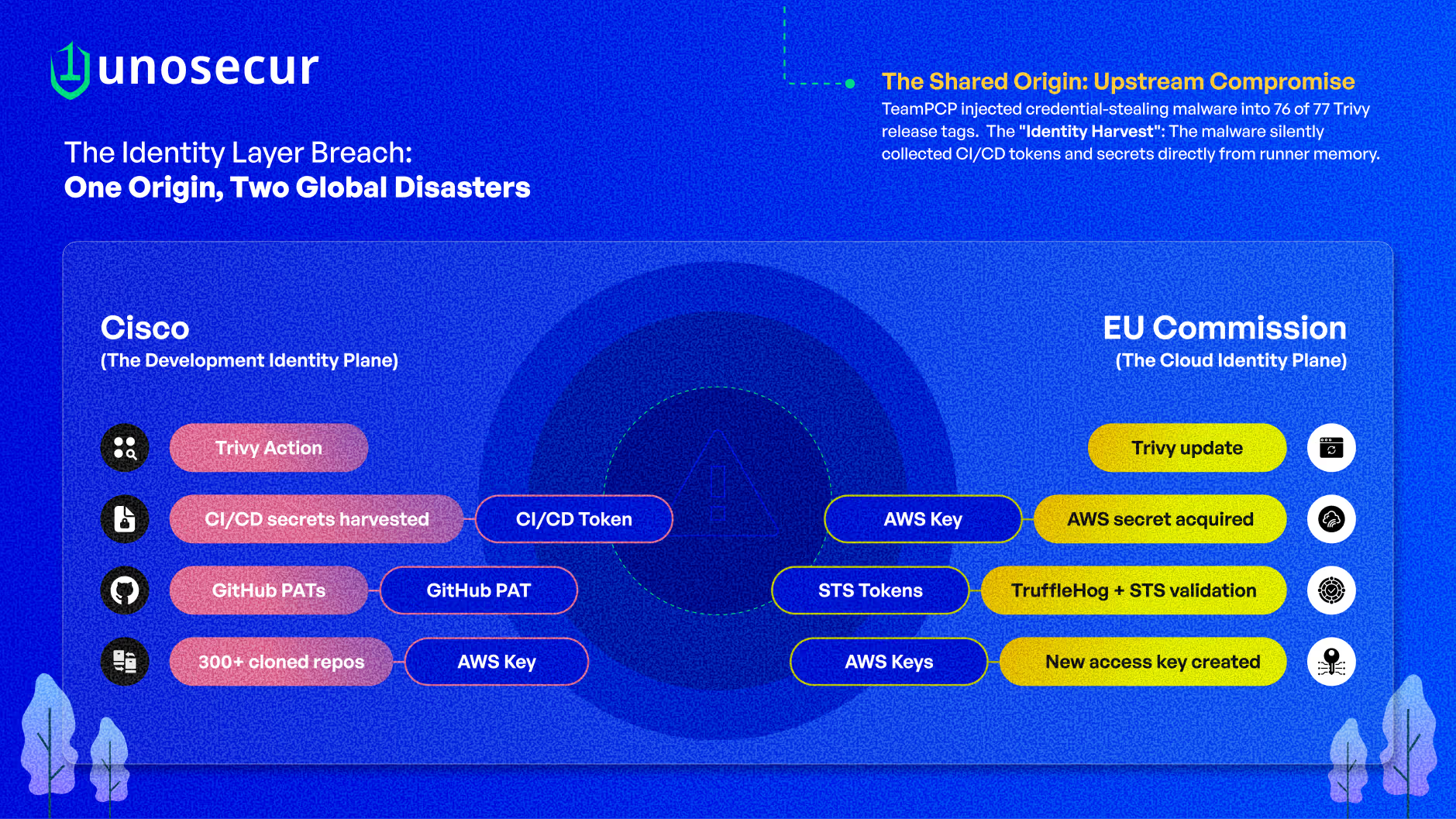
In March 2026, two of the world's most prominent organizations, Cisco and the European Commission, were breached within days of each other. Different environments. Different continents. But the same upstream compromise, the same threat actor, and the same fundamental failure. Attackers didn't exploit a vulnerability. They used valid credentials, stolen from CI/CD pipelines, to log into trusted systems and take what they wanted. At Cisco, the breach reached source code, cloud infrastructure, and customer-linked assets. At the European Commission, it reached the backend of europa.eu, exposing data across dozens of Union entities. Neither organization was broken into. Both were logged into.
Cisco: When stolen pipeline credentials unlock the enterprise
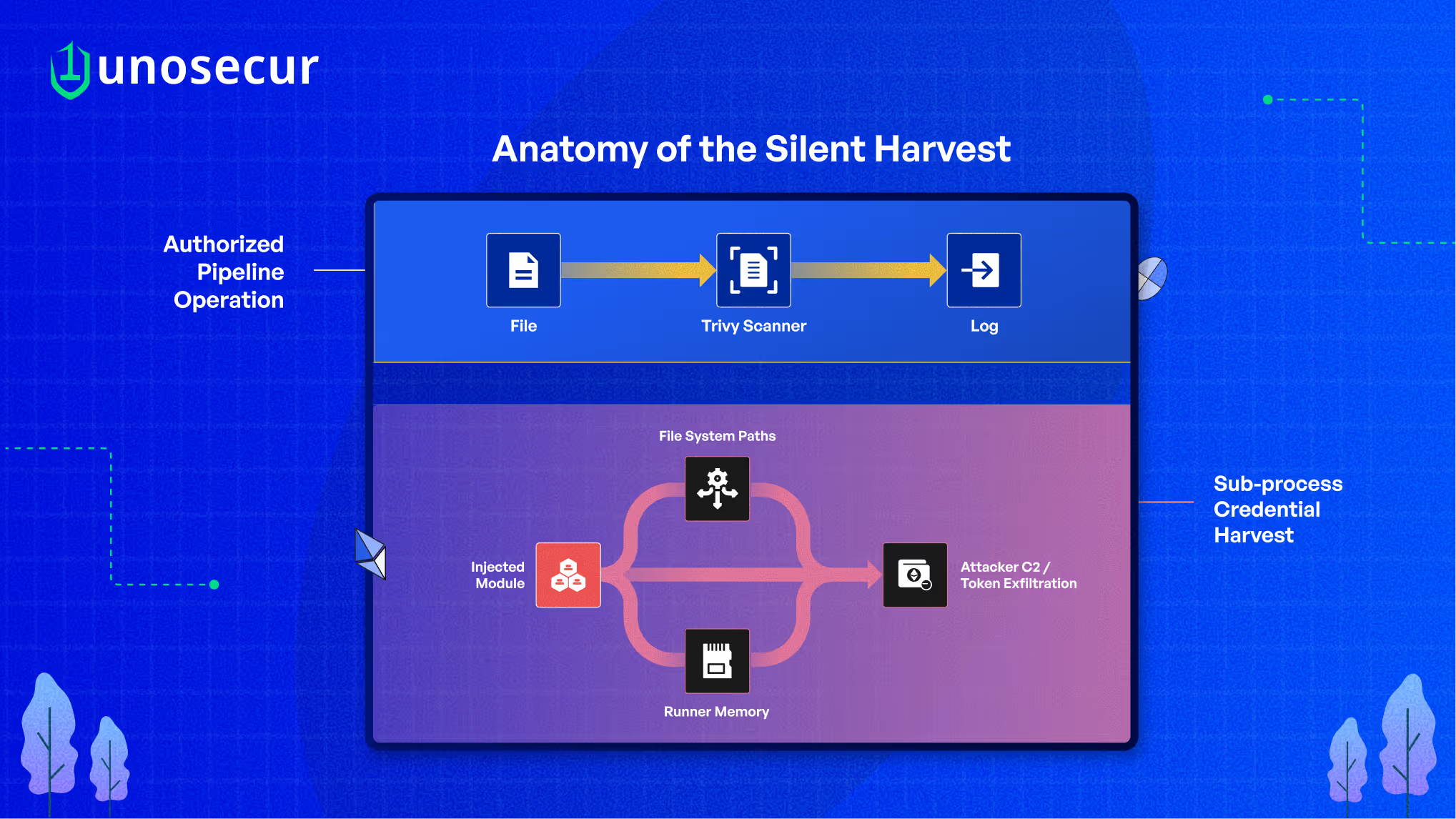
The Cisco breach started quietly, inside a CI/CD pipeline running a routine security scan. Cisco's development environment used Trivy, a widely adopted open-source vulnerability scanner. In March 2026, attackers from a group called TeamPCP had compromised Trivy's official releases, injecting credential-stealing malware that ran silently before the real scan. The legitimate scan still produced normal output. Nothing looked wrong. But the malware had already done its job: it collected every credential it could find in the build environment, including tokens, cloud keys, access secrets, and sent them to the attackers.
Those stolen credentials gave attackers authenticated access to Cisco's internal systems. What followed was systematic. Over 300 GitHub repositories were cloned, including source code for AI Assistants, AI Defense, and unreleased products. A portion of these reportedly belonged to corporate customers: banks, BPOs, and US government agencies. AWS keys were stolen and used to carry out unauthorized activity across Cisco cloud accounts. Dozens of devices were impacted, including developer workstations. Cisco's security teams contained the breach but acknowledged continued fallout. Credential rotation and system reimaging are underway. Then the extortion began.
On March 31, ShinyHunters posted demands with an April 3 deadline, claiming over 3 million Salesforce CRM records containing personal data, alongside AWS infrastructure assets. They described three separate access paths into Cisco's environment, suggesting possible collaboration between two distinct threat groups converging on the same victim. No exploit chain. No zero-day. The pipeline executed exactly as designed. The credentials it exposed did the rest.
The European Commission: When one cloud key opens an entire infrastructure
Five thousand miles away, the same upstream compromise was unfolding against a very different kind of target. On March 19, the European Commission unknowingly pulled the same compromised version of Trivy through normal software update channels. But where the Cisco breach played out across development infrastructure, the European Commission breach cut straight to the cloud. The attackers acquired a single AWS credential with management rights over affiliated cloud accounts. That one key was all they needed.
They validated it, confirmed it was live, and then used it to create a new access key attached to an existing account, giving themselves persistent access that would survive a password reset. Then they mapped the environment and began pulling data. Five days passed before the European Commission's security operations center detected unusual activity. By then, roughly 340 GB of data had already left the building. The compromised cloud account powered multiple public websites of the European Commission. Forty-two internal European Commission clients and 29 other Union entities were impacted. ShinyHunters published the dataset on their dark web portal: names, usernames, email addresses, and over 51,000 files of outbound communications.
A critical detail from the official CERT-EU advisory: the attackers had the access rights to move into additional European Commission cloud accounts. They chose not to. The damage was bounded by the attacker's decisions, not by any security control. The cloud wasn't breached through a vulnerability. The identity controlling it was compromised. One key. Seventy-one entities. Three hundred and forty gigabytes. No exploit required.
The shared story
Two breaches. Two continents. One playbook. In both environments, a trusted CI/CD tool silently collected the credentials it was never supposed to touch. The malware didn't need to escalate privileges or exploit a system flaw. It simply gathered what was already there: tokens, cloud keys, and access secrets sitting in the build environment, accessible to any process running in that context. From there, the pattern mirrored itself. At Cisco, stolen credentials unlocked repositories, then cloud accounts, then reportedly customer-facing platforms. At the European Commission, a single cloud key with management rights opened access across affiliated accounts.
In both cases, every action after the initial theft was authenticated. Valid credentials. Authorized operations. No alerts. The divergence was only in what the attackers chose to take. At Cisco, source code and customer-linked assets. At the European Commission, 340 GB of infrastructure data across 71 Union entities. But the mechanism was identical: the blast radius was defined not by what was vulnerable, but by what the compromised identities were permitted to reach. The pipeline didn't fail. It authenticated the attacker.
What attackers are really after, and why no one saw it coming
These breaches confirm a shift that's been building for years. Attackers aren't focused on finding software vulnerabilities anymore. They're targeting the credentials that control the pipeline: build tokens that grant access to everything the pipeline touches, service accounts that persist indefinitely without anyone watching them, cloud keys that unlock entire environments with a single authentication, and code access tokens that let you clone repositories and push changes. At Cisco, these credentials unlocked the development environment and everything connected to it. At the European Commission, a single cloud key with broad permissions enabled access to 340 GB of data across dozens of entities. The reason is straightforward: a valid credential within a pipeline grants more access with less scrutiny than any exploit ever could.
And that's exactly why no one saw it coming. At both organizations, the post-compromise activity looked completely normal to security tools. At the European Commission, the security team detected unusual activity five days after the initial compromise, by which point the data was already gone. At Cisco, internal teams contained the breach but expect continued fallout. Every action, cloud enumeration, repository access, and data download was performed with valid credentials, doing things those credentials were authorized to do.
Traditional security tools are built to catch exploits, malware signatures, and network anomalies. These attackers used none of those things. The activity was only abnormal if you knew what those specific identities should have been doing. But machine identities, the service accounts, tokens, and automation credentials that run modern pipelines, outnumber human users by orders of magnitude. They're provisioned, granted broad access, and forgotten. No one models what "normal" looks like for them. So no one notices when they start behaving abnormally.
The damage followed the permissions
The impact in both cases wasn't random. It followed the access encoded in the stolen credentials. At Cisco: pipeline credentials → 300+ repositories (including customer code for banks and government agencies) → cloud accounts → reportedly 3 million Salesforce CRM records. Each hop authenticated, each system unlocked by the permissions of the credential before it.
At the European Commission: a single cloud key with management rights → backend access to multiple public European Commission websites → 340 GB across 42 internal clients and 29 Union entities. The attackers had the right to go further. They chose not to. The damage was bounded by their decisions, not by any architectural control. One upstream compromise. Two credential chains. Hundreds of downstream systems.
This is a pattern, not an incident
Cisco and the European Commission were only the most visible victims. The same identity-layer targeting is playing out across the entire software supply chain, across ecosystems, threat actors, and continents. TeamPCP's own campaign extended to four open-source tools in eight days: Trivy, Checkmarx KICS GitHub Actions, LiteLLM on PyPI, and the Telnyx Python package, all deploying the SANDCLOCK credential stealer targeting pipeline secrets, cloud credentials, and API keys. The LiteLLM compromise specifically targeted an LLM gateway that stores API credentials for multiple model providers, meaning a single compromised host could expose keys to every AI service the organization uses. Google Threat Intelligence now tracks TeamPCP as UNC6780.
The Axios npm package, one of the most widely used JavaScript libraries with over 100 million weekly downloads, was compromised through a maintainer account takeover. Google Threat Intelligence attributed this to UNC1069, a financially motivated North Korea-nexus threat actor. The attackers injected a malicious dependency that deployed the WAVESHAPER.V2 backdoor across Windows, macOS, and Linux, a fully functional RAT capable of reconnaissance, command execution, and credential harvesting at scale. State-level actors targeting the same identity layer as cybercriminals. The Nx build system compromise followed a similar path: a stolen npm publishing token gave attackers the ability to push infostealer payloads that exfiltrated GitHub tokens, SSH keys, and cloud credentials from every organization that installed the compromised packages.
Shai-Hulud 2.0 demonstrated the recursive loop that makes identity compromise self-amplifying. Compromised npm packages stole GitHub, AWS, and GCP credentials, then used those stolen publish tokens to infect more packages, which stole more credentials. Over 25,000 exfiltration repositories were created, roughly 1,000 every half hour at peak activity. The campaign spread from npm to Maven, crossing ecosystem boundaries. GlassWorm planted obfuscated packages across GitHub, npm, and VSCode to harvest NHI tokens and service keys, the same class of machine credentials that gave TeamPCP access to Cisco's repositories and the European Commission's cloud accounts.
Every campaign enters through a different door. Every campaign targets the same thing: the machine identities that control development infrastructure. Cybercriminals, nation-state actors, self-replicating worms, all converging on the identity layer. Different ecosystems, different threat actors, same structural failure. Attackers don't break in. They log in.
Where Unosecur fits
Both breaches trace back to the same structural weaknesses: fragmented visibility across identity systems, credentials carrying far more access than needed, incomplete rotation that left residual access paths open, and no behavioral monitoring to catch valid credentials being used in abnormal ways. Unosecur operates at the identity layer where these attacks execute.
Unified Identity Fabric (UIF)
UIF is a unified orchestration layer across cloud, SaaS, identity providers, and CI/CD systems. It doesn't replace your existing identity tools. It connects and normalizes them, providing a single view across AI agents, NHIs, and human identities. In the context of these breaches, visibility into credentials that survive rotation, like the service account that enabled the entire Trivy re-compromise. Mapping how a single credential chains across systems so the blast radius is understood before an attacker finds it. Identifying dangerous permission combinations, such as a cloud key with management rights over affiliated accounts, that turn a single stolen credential into cross-environment access. Most identity tools see one layer: cloud IAM, or SaaS, or the identity provider. They don't see how a credential in a CI/CD pipeline chains to a cloud account that connects to a SaaS platform. UIF connects all of them, which is why it surfaces the cross-environment risk that single-layer tools structurally miss. UIF reduces the exposure surface and helps identify the identity risk that attackers rely on.
Identity Threat Detection and Response (ITDR)
Unosecur's ITDR monitors how identities behave: token usage, API activity, privilege changes, and access patterns. It detects anomalous activity that traditional security tools are structurally blind to, because those tools look for malware and exploits, not credential misuse. In the context of these breaches, detecting when credentials are being tested from unfamiliar locations. Flagging when new access keys are created on existing accounts, the exact persistence mechanism is used against the European Commission. Recognizing when a service account suddenly begins accessing resources far outside its normal scope. When anomalous behavior is detected, ITDR enables response at the identity layer: revoking tokens, disabling accounts, and providing the context needed for investigation. This reduces dwell time and helps contain the blast radius before it extends across environments.
The shift
From Cisco's development pipelines to the European Commission's cloud infrastructure, the pattern is the same. Attackers aren't breaking systems. They're using the trust encoded in machine identities. They aren't exploiting vulnerabilities. They're presenting valid credentials. They aren't intruding. They're authenticating. The development pipeline is identity infrastructure. The cloud is identity infrastructure. The control plane of modern systems is identity. From Cisco's pipelines to the European Commission's cloud, the attacker didn't break in. They logged in. If your CI/CD tokens can reach your cloud accounts, your source code, and your SaaS platforms, do you know what the blast radius looks like if one of them is compromised?



.avif)
.avif)




