OAuth Token Theft via Redirect Manipulation

Executive summary
OAuth token theft via redirect manipulation is an identity-layer attack that exploits weak redirect URI validation in applications using third-party authentication, such as social login. Instead of stealing passwords, attackers intercept OAuth authorization codes or access tokens and reuse them to log in as victims. This threat primarily impacts SaaS platforms, developer tools, and enterprise applications relying on OAuth-based SSO where redirect URI validation is improperly configured. The severity is high because it bypasses strong passwords and MFA entirely. This is not a credential compromise issue. It is a trust-validation failure. Organizations must secure not just authentication mechanisms but also how OAuth tokens are issued, validated, and monitored.
What is the threat about
This threat stems from unsecure OAuth implementation, specifically improper redirect URI validation.
Attack flowThe attack begins when an attacker crafts a malicious OAuth login link and delivers it to a victim. The victim then authenticates normally with the identity provider, at which point the application fails to strictly validate the redirect URI. As a result, the authorization code or access token is redirected to an attacker-controlled domain, where the attacker reuses the valid token to access the victim's account. It is important to note that the identity provider itself is not compromised. The weakness lies entirely in the relying application's configuration.
Threat classificationThis attack is classified as identity token interception, account takeover (ATO), and session hijacking.
Why it emergedThe rapid adoption of OAuth-based SSO for usability has led to inconsistent implementation practices across organizations. Common weaknesses include the use of wildcard or loosely validated redirect URIs, missing PKCE enforcement, and over-permissive OAuth client configuration.
What is the impact of the threat
Operational impact From an operational standpoint, this threat enables unauthorized account access, data exposure within SaaS platforms, and the abuse of legitimate user sessions.
Financial impactFinancially, organizations face incident response and forensic costs, regulatory risk if sensitive data is accessed, and potential fraud exposure depending on the nature of the compromised accounts.
Reputational impactOn the reputational front, a successful attack can result in a significant loss of customer trust and a public perception of authentication weakness within the organization.
Strategic impactAt the strategic level, the consequences include intellectual property theft and long-term unauthorized access to internal platforms. Because the login appears legitimate in authentication logs, detection is inherently difficult, significantly increasing attacker dwell time within compromised environments.
Root Cause Analysis (RCA)
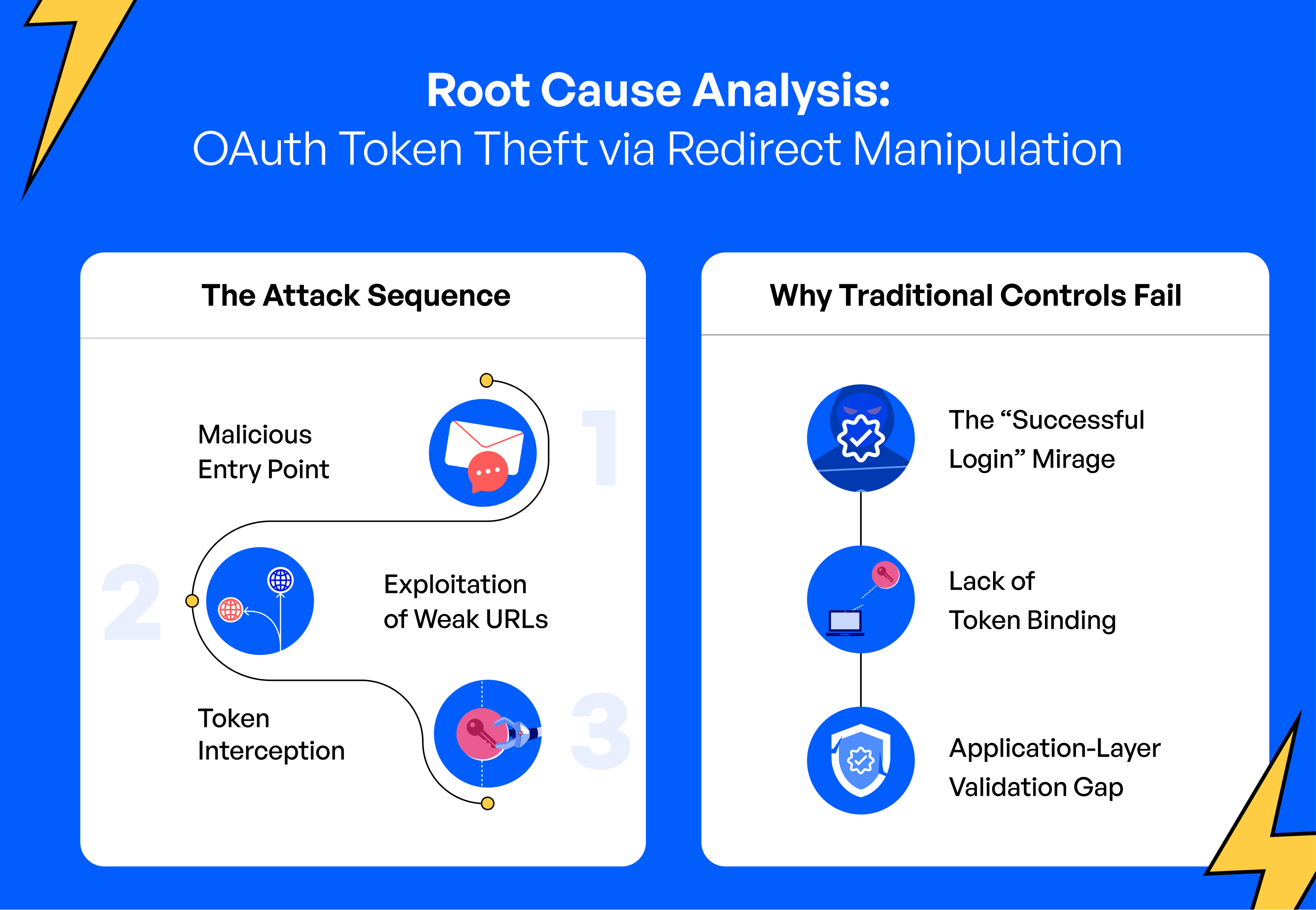
Entry pointThe attack is typically initiated through user interaction with a crafted OAuth login link, delivered via phishing, chat messages, or embedded content.
Exploited weaknessThe core weaknesses being exploited include weak or wildcard redirect URI validation, a lack of strict allowlist enforcement, the absence of PKCE, and the use of long-lived tokens.
Why controls failedControls fail in this scenario for several interconnected reasons. Authentication logs record a successful login, meaning no immediate alert is triggered. There is no monitoring in place for abnormal token usage, no token binding to a specific device or client, and limited behavioral anomaly detection to catch post-authentication irregularities. This is primarily an application-layer validation gap rather than a failure on the part of the end user.
Detection and mitigation strategy
DetectionSecurity teams should monitor for OAuth responses redirecting to unrecognized domains, sudden geographic or device shifts following an OAuth login, multiple token redemptions originating from different IP addresses, and abnormal OAuth client usage patterns. Key log sources for this monitoring include identity provider logs, application access logs, and reverse proxy or WAF logs.
MitigationAs immediate actions, organizations should enforce strict exact-match redirect URI allowlists, revoke any suspected access and refresh tokens, and rotate credentials where necessary. For longer-term hardening, teams should enforce PKCE across all OAuth flows, eliminate all wildcard redirect URIs, adopt short-lived tokens, and bind tokens to client or device context wherever feasible.
PreventionOn a preventive basis, organizations should conduct periodic OAuth configuration audits, integrate secure SDLC validation of authentication flows, and establish continuous identity behavior monitoring as an ongoing practice.

How Unosecur helps
OAuth token abuse is fundamentally an identity misuse problem that requires deep behavioral visibility to address effectively. Unosecur supports defense by monitoring authentication behavior for anomalies, detecting suspicious post-OAuth login activity, identifying abnormal geolocation and device shifts, alerting on token misuse patterns indicative of account takeover, and providing centralized visibility into identity risk across SaaS environments. This ensures that identity security extends well beyond passwords to encompass the full token lifecycle.
Conclusion
OAuth token theft via redirect manipulation demonstrates that strong authentication alone does not guarantee secure access. As organizations continue to expand their OAuth and SSO integrations, misconfigurations create silent but high-impact identity risks that can go undetected for extended periods. Security strategy must evolve to enforce strict redirect validation, monitor token usage behaviorally, and treat identity as a continuously monitored control plane rather than a one-time checkpoint. Authentication is only the first step. Trust validation must persist throughout the entire session lifecycle.
Don’t let hidden identities cost you millions
Discover and lock down human & NHI risks at scale—powered by AI, zero breaches.