TL;DR
A new Shai-Hulud-style npm supply chain attack has compromised a significant number of open-source packages by hijacking maintainer accounts and publishing malicious versions. These tampered packages executed malware during the pre-install phase and quietly exfiltrated cloud credentials, GitHub tokens, and CI/CD or automation secrets into attacker-controlled GitHub repositories. More than 25,000 repositories were created to store the stolen data. At peak activity, almost one thousand new repositories appeared every half hour. This blog reframes the incident from a cloud identity perspective and outlines how a strong identity posture, supported by Unosecur, reduces the long-term blast radius.
What Happened
Compromised npm Packages
Between November 21 and 23, 2025, attackers released malicious versions of popular npm packages. Because these packages were already embedded across enterprise codebases, CI pipelines, developer machines, and production build systems, the malware spread quickly without raising immediate suspicion.
Mass Credential Exfiltration
Once installed, the infected packages launched credential harvesting at scale. The malware scraped cloud keys, GitHub tokens, CI/CD and pipeline secrets, environment variables, metadata tokens, and configuration files. It generated JSON files such as environment.json and cloud.json and uploaded them into the attacker-owned GitHub repositories. This activity occurred repeatedly inside CI/CD systems, causing many credentials to appear multiple times.
Scale of Exposure
The exposed data included hundreds of GitHub tokens and cloud provider credentials across AWS, GCP, and Azure. Because installations happened inside automated systems and developer laptops, the malware captured both long-lived secrets and temporary session tokens. The breadth of this exposure created a scenario where stolen identities could be reused across environments with little friction.
How the Malware Captured, Abused, and Propagated Cloud Identities
Preinstall Execution
The malicious packages relied on a pre-install script that executed the main payload before the package was even installed. Any environment that invoked npm install triggered the malware, making developer laptops and CI/CD systems equally vulnerable.
Credential and Environment Harvesting
The malware gathered GitHub tokens, cloud provider credentials, metadata tokens, npm publish tokens, CI/CD variables, SSH keys, browser artifacts, and recursively scanned the user’s home directory. This broad harvesting created a deep pool of credentials that attackers could reuse across multiple cloud accounts.
Data Exfiltration via GitHub
After collecting the data, the malware created new public GitHub repositories using stolen tokens. It uploaded the harvested JSON files and often used multiple victims as upload nodes, mixing their data to hinder attribution.
GitHub Workflow Backdoor
Infected machines were registered as self-hosted runners labeled SHA1HULUD. The malware also added a workflow that executed incoming discussion events as shell commands, creating a persistent execution channel tied to GitHub infrastructure.
GitHub Secrets Exfiltration Workflow
The malware inserted a temporary workflow that enumerated all repository secrets, serialized them, pushed them as GitHub Actions artifacts, and then removed itself. This allowed attackers to collect secrets even from projects that did not install the compromised package directly.
Supply Chain Propagation
Using stolen npm tokens, the malware downloaded every package owned by a compromised maintainer, injected the preinstall script, bundled the payload, incremented the version, and republished it. This created a worm-like spread through the npm ecosystem.
Lateral Propagation Using Stolen Tokens
The malware repeatedly scanned stolen data for more tokens and cycled through available credentials. It reused tokens from different victims to fan out across multiple accounts and increase its resilience.
Destructive Fallback Behavior
When exfiltration or replication failed, the malware switched to destructive behavior. On Windows, it deleted files and attempted disk overwrites. On Linux and macOS, it recursively performed secure deletion of user directories.
Container Breakout Attempt
The malware attempted to escape containers by launching a privileged Docker run that mounted the host filesystem. If successful, it injected a sudoers file granting passwordless root access, turning the container compromise into a host compromise.
Cross Victim Exfiltration
The malware deliberately mixed data from different victims across multiple repositories. This strategy complicated forensic analysis and ensured that even if one repository was removed, portions of the data would remain elsewhere.
What Security Teams Should Do
Remove Malicious Packages
Security teams should clear npm caches, delete node modules, and reinstall versions released before November twenty one, 2025. This ensures that the malicious preinstall hook can no longer trigger inside build systems or developer environments.
Rotate All Credentials
Every cloud provider key, GitHub token, CI/CD credential, npm token, and SSH key exposed through the malware must be rotated. Delayed rotation increases the window during which attackers can continue to use compromised identities.
Audit GitHub Activity
Teams should review repositories for references to Shai Hulud, unauthorized workflows, unrecognized self-hosted runners, and suspicious branches. These artifacts reveal whether the malware established persistence inside GitHub environments.
Harden Build Pipelines
Teams should disable unnecessary lifecycle scripts in build systems, restrict network access in CI/CD, pin dependency versions, and rely on short-lived scoped credentials. These measures reduce the reach of future supply chain attacks.
Evaluate Cloud Identity Posture
The final step is long-term improvement. Organizations need to map leaked credentials to specific identities, analyze permissions, find excessive privileges, monitor identity behavior, and remediate misconfigurations. This is where identity posture becomes the primary defense against repeat incidents.
The Cloud Identity Security Dimension
The attack directly targeted the heart of cloud identity infrastructure. The malware read local cloud configuration paths, scraped CI/CD environment variables, queried metadata services, and accessed cloud secret stores whenever credentials were available. With valid tokens in hand, attackers could pivot across services, read sensitive production secrets, move laterally, escalate privileges, and even create long-lived persistence. The scale of damage depended entirely on the privilege spread and hygiene of the compromised identities.
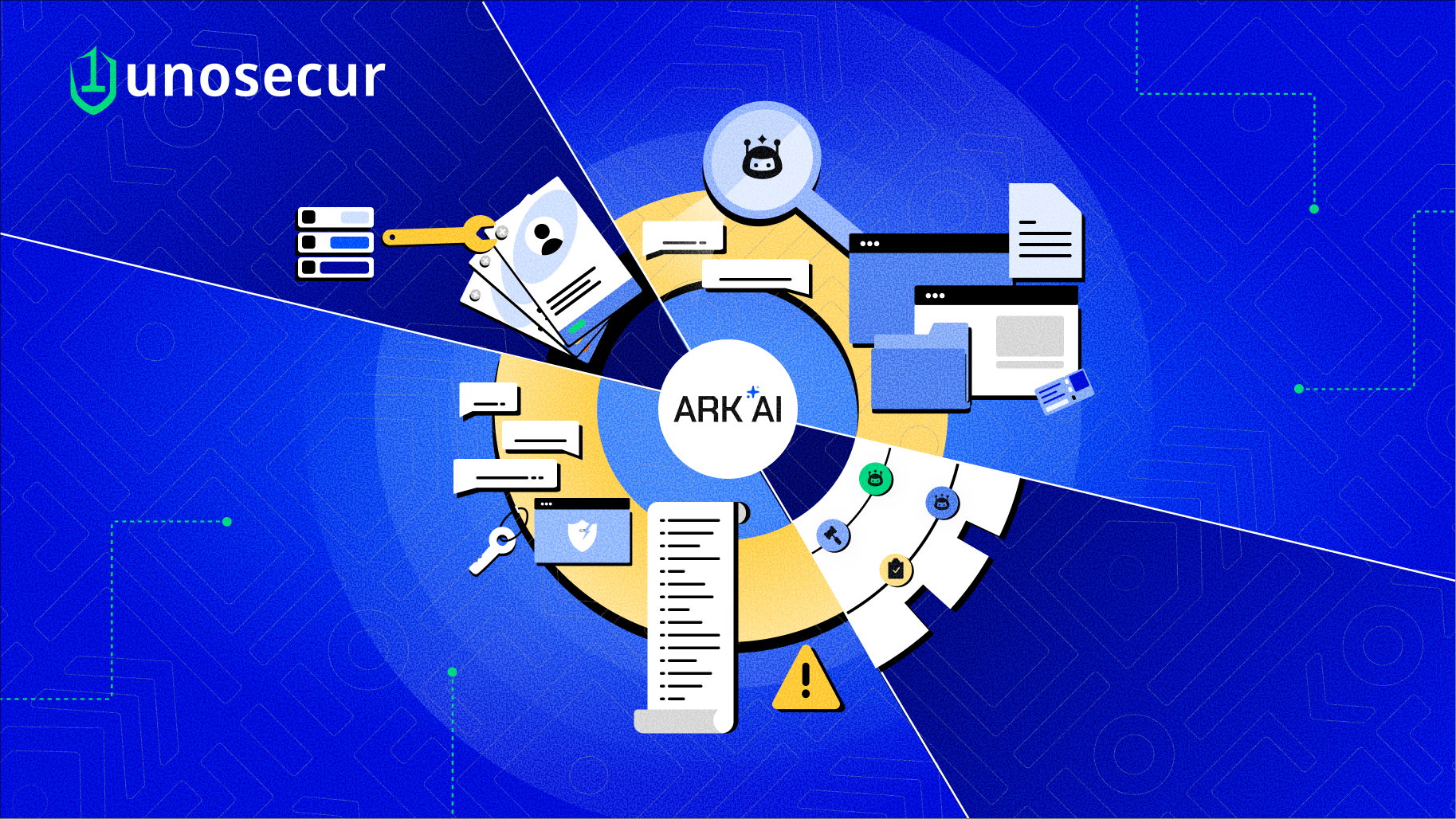
How Unosecur Fits Into the Cloud Security Response
Unosecur provides the identity visibility, behavioral monitoring, and privilege analysis needed to understand and contain the ripple effects of a supply chain breach. It offers a single view of cloud identities and their relationships, surfaces high-risk privileges, detects suspicious activity, and guides posture cleanup. These capabilities align directly with the core questions security teams must answer when facing a compromise of this magnitude.
1. Understanding Cloud Identity Exposure
The first critical step is mapping each leaked credential to a real identity. Teams must determine which exposed tokens belong to production roles, which automation accounts carry elevated permissions, and which identities can assume additional roles. Unosecur’s identity relationship mapping helps correlate leaked keys to their privileges and quickly identifies the identities that present the highest risk if abused.
2. Detecting Possible Misuse of Cloud Credentials
The malware attempted unauthorized role assumptions, temporary token use, secret store access, and silent modifications to privileges. These actions often blend into normal cloud logs and can be hard to detect in real time. Behavior-based monitoring highlights unusual identity activity such as suspicious role chaining or unexpected access requests, helping security teams reveal misuse linked to compromised identities even after log noise or partial data loss.
3. Reducing Blast Radius Through Identity Posture Improvements
The overall impact of Shai Hulud 2.0 was shaped by excessive privilege spread across cloud environments. When service accounts or human identities carry broad or unused permissions, attackers gain far more power once a credential leaks. Identity posture improvements reduce this risk by identifying overly permissive roles, eliminating unnecessary privileges, replacing long-lived credentials with short-lived alternatives, and hardening service accounts. Unosecur supports this long-term resilience by continuously highlighting misconfigurations and privilege bloat.
4. Supporting Credential Revocation and Cleanup
Once a compromise is confirmed, the cleanup workload becomes extensive. Teams must revoke access keys, regenerate cloud provider secrets, rotate GitHub tokens, update CI/CD credentials, reset SSH keys, and confirm that the attacker did not create new identities, roles, or hidden access paths. Identity relationship views ensure that cleanup is complete across every provider and prevent missed tokens from becoming long-term backdoors.
Closing
The Shai Hulud 2.0 campaign shows how quickly a supply chain compromise can escalate into a cloud breach through aggressive credential harvesting and identity propagation. By strengthening identity posture through visibility, behavioral monitoring, and privilege remediation, organizations can significantly reduce the long-term risk of similar attacks.




.avif)